Put your Computer in Sandbox
Believe it or not, when you type a web site’s URL in your browser’s address bar and push Go button to surf that site, you do not go to that web site, but the site actually come to you. Fancy graphics, flashy animations and all kinds of auto-executable codes that includes ActiveX controls and Java Applets gets download on your computer and run there and display the results as stunning, interactive and informative web pages in your web browser’s window. Further, can you believe that these auto-executable codes are capable to perform practically any task- repeat- any task in your computer with or without your knowledge! The real security threat comes to you because of your own act- that is surfing to those sites that may contain malicious ActiveX control or Java applet or any other code that can be a worm or a virus embedded in its HTML page! Now what do you do to safe guard your computer from these?
Towards a safer Internet
You cannot live without Internet. Moreover, in future, all computers (optimists believe that all future appliances) will be connected to Internet any way. As a security measure, you can easily disable running scripts and auto-executable code from your browser settings, but then your web experience will be dead enough, you cannot tap Internet’s full potential and very purpose of Internet is defied. As a Security measure, you can reject all email attachments, turn off ActiveX, Java, JavaScript and VBScripts in your email and browsers and disable Macros in Office applications. What will happen now? You will revert back to ancient age of computing and your productivity will be seriously hampered and your survival in IT field will be jeopardized. As a user, your experience with web pages will be static plain text and dead graphics without any interactivity. Similarly, installing Virus scanner or Firewalls in your computer may not work always. Virus Scanners takes reactive approach to identify Viruses, Worms and Trojan Horses by matching signature database of known viruses. Hence a new kind of Virus that has no known signature database existing, can spread undetected like wild fire. Scanning for viruses and removing after detection worked well in the past when most infection caused through exchanged Floppies and are very slow in spreading; thus before a virus spreads to a potential area, an antidote is worked out and damages are arrested to a great extent. But in this era of Internet, a self replicating virus having multiple strains can spread to hundreds of thousands of computer world wide in no time. Viruses and worms may spread not only through your email attachments but will also spread through your browser and instant messaging programs. Instant messaging services which are among most popular Internet services presently, are most risky applications since users chat in real time; bypassing email servers, filters, firewalls and can download and transfer files that can contain malicious code. Even web enabled cell phones have been attacked by viruses. By the time antidote for the virus is worked out, it can already make intended damages. Further, if a known virus is altered slightly even as compressed zip files, its binary signature is altered thus making its detection by virus scanner, harder. Even your trusted sites that you have permitted in your firewall setting can innocently push malicious code. It seems that there is no way out to tap all potentialities of Internet without fear of damages. No, I bet, yes, you have!
New, Proactive approach
Often, some problems are solved with proactive approach that includes creating simulated conditions in protected, closed environment for studying and analyzing problems and working out for possible solutions. If this approach is applied to the content of Internet that you are using, then potential threat that the web content can do could be studied. The contents are then passed {or failed if not satisfy certain conditions} for further use. This technique is called Sandbox technique, which is a proactive approach to stop the malicious actions of internet code before any malicious activity can occur. The Sandbox application sits between the malicious code and the operating system and intercepts any system calls that code made. It checks its policy database to determine just what the kind of code is allowed to perform certain kind of task and immediately block any unauthorized activity. The Sandbox technique allows Internet’s active content (or any application, known or unknown) to run in a closed, controlled and isolated or virtual machine environment thus create an impenetrable barrier between the suspected content that is running and rest of your computer’s data and operating system. Within this closed environment (Sandbox) any code can run and access calls to system resources, services including change in registry databases but are only allowed within the set precondition to protect the privacy and integrity of your computer. In sandboxing techniques, all the active contents that are being downloaded off Internet through any means are tracked. Then the requests for system resources and services are intercepted and compared to a pre defined set of system policies. If policy violations are not detected, suspicious or unwanted activities are not found, then requests are allowed, else denied or prompted (if you set it so) for your clarifications. According to set rules, the actions of downloaded active content determine whether it is allowed for further running and performing further task or stopped. The Sandbox applications are behavior checker that checks for hostile attacks; also isolate buggy application and deny each and every action for system resources or services whether arises locally or across network if it is set specifically to not allow. This way, any application, even unsecured one along with their entire feature, Web content, email and chat clients, Messenger services, Web Browsers or virtually any other code (including potentially dangerous codes) can run safely (without creating intended damages, since they are stopped by sandbox before their malicious act) in your computer if there is Sandbox software installed.
Now what happens when a new, unknown virus, worm, malicious ActiveX control or Java Applet sneak in to your computer that is protected with sandbox; and try to perform some malicious activity? Since Sandbox software is watching every call for system resources and system services in real time, and sometimes these codes are run in protected, sandbox’s virtual environment, according to sandbox’s access control set policy, activities are allowed, stopped or prompted you for your approval. For example, an e-mail attachment having unknown virus can be safely tamed by sandbox even after opening the attachment if it tries to install, copy or change any thing in your computer with or without your knowledge. This proactive method of protecting access control of codes and applications makes Sandbox Technology a promising, futuristic one. Without having any Virus definition files, a Sandbox application can stop age old C-brain virus, as well as latest Worm- Klez and even the viruses and malicious codes of future that have not discovered yet. The only limitation here is security hole itself in the Sandbox application if there is any. Sandbox technology does not need frequent updating unlike Virus Scanners. In most of the cases, Sandbox technology does not concern with new technology or new application either. Even with the case of new programming language, if the system resources or services are defined to be not allowed to any outsider application or codes than all such services will not be allowed no matter how genuinely and repeatedly they try.
Flexible Security Policies
Sandbox technology offers you security policies that are extremely flexible, broad can be customized to individual user and application level. Different policies could be assigned as per security requirement for different people, groups, resources, active contents etc. The Sandbox can be managed from a central location and can also log events relating to any type of content execution. Take for example, if you want your data fully protected by unauthorized access from ActiveX or Java Applet, then it could only be accessed by traditional methods allowed by Sandbox. Any attempt made by any other application or code will be instantly terminated.
Virus Scanner or Sandbox
In securing your computer, Sandbox software works better than antivirus software because it scans for the actions the virus code takes and not the name or characteristics of virus. With some advanced Sandbox application, you can find out from which site it was downloaded, and how it interferes with your computer. Though it may be fully capable to protect your computer, Sandbox software cannot tell you which virus type you have in your computer neither it can remove the Virus that had sneaked in. It can only tell that you have some suspected, malicious piece of code that can do unwanted things in your computer and protect you from it if you have properly set policies. Pattern matching technology and Virus removing technology that Virus Scanner have can only tell and remove the type of Virus you have. The sandbox technology cannot replace Traditional antivirus scanners, as identification, disinfection and removal of viruses can only be done by virus scanners. However, Sandbox and Virus Scanner can work complementary to each other for providing a fully secure environment. That is why Virus scanner companies like Symantec, F-secure, MacAfee and Trend Micro are adding behavior blocking Sandboxing technology in their Anti virus security software that provides you Antivirus, content filtering and behavior blocking all rolled in one. With Virus scanner installed that sandbox application supports, Known virus can be scanned, unknown virus can be detected and can be removed. So far, the best approach is to have sandbox technology and antivirus both.
Presently, Sandbox software is being developed by small software companies like Finjan Software Ltd (SafeTnet), Pelican Software Ltd (SurfinGuard), Aladin Knowledge Systems Ltd. (eSafe) Etc., but as the concept start delivering things, big fish will definitely jump in the wagon. One promising application is Norman’s new sandbox technology that creates a virtual computer within the computer and then run the codes and applications in virtual pretended environment. Suppose a deadly virus is run completely in virtual environment, which sends email with its replicas, format hard drive, and then flashes BIOS. Since all these things happen in virtual, isolated environment, it does not make any effect in real computer. Moreover, entire process is logged for reference and further analysis. Running sandbox in virtual machine makes it platform independent and you can detect a Windows virus in a Linux machine. Here, sandbox software SafeTnet and SurfinGuard are reviewed for you.
SurfinGuard
Finjan Software’s SurfinGuard, the premier Sandbox software that protects your computer from Internet’s malicious codes as well as computer’s installed applications is fairly easy in use. It has very user friendly interface for security policy settings that needs to be customized for required level of security. It comes with default Medium security settings. It needs Java run time environment installed in your computer (it comes with one) so that it can test applets and scripts whether trusted or not. SurfinGuard supports Latest Windows XP operating system. To define security setting in SurfinGuard, right click in its system tray icon and click advanced. Then fine tune individual settings. Once its security settings are defined, it starts with Windows and constantly run in background unless you turn it off. It shows current running process, application and websites in its dock able menu bar. If it detects policy violations, it instantly shows visual and sound alert. You can set individual security settings for executable programs and codes, ActiveX, Java Applets and JavaScript etc. with SurfinGuard, you can also monitor and control behavior of Host application that includes FTP, Instant Messenger, Mail Client etc. There is a Panic Mode by which you can block all active content of your computer instantly. Any executable file can be run in safe mode, i.e. in SurfinGuard’s protected, sandbox environment. During testing, it detected and stopped slightest policy violations performed by a web site like reading file from your computer (apparently a cookie file). You can download evaluation version of this software from http://www.finjan.com
SafeTnet
Pelican security’s sandbox software- SafeTnet is powerful security tool that protects you from all kinds of malicious activity and virus infection that you may get from Internet. It can monitor host application as well as email clients, FTP clients, Instant Messengers, Web browsers and other Web applications. SafeTnet has a dynamic Sandbox where the active content is executed and monitored; the activity is then compared with security policies and then passed or blocked accordingly. SafeTnet alerts you when a suspected application is started prior to SafeTnet or not supported by it and hence is not monitored by it. In SafeTnet, you can define trusted web sites and applications to exclude monitoring from SafeTnet to speed up things, since monitoring constantly in background may slow down system speed. SafeTnet’s custom security settings let you assign to allow, deny or prompt for action for virtually every file manipulations and running application in your computer. It also supports remote security management and can send you alert email automatically informing you for policy violations. SafeTnet comes with neat help function where you can quickly learn to use the application. It starts with Windows and sits in system tray constantly watching every action of your computer in background. SafeTnet’s menus are accessed by right clicking its system tray icon. It has a built in function that shows status of monitoring running applications and Internet Client.
Trial version of this software can be downloaded from http://www.pelicansecurity.com
It seems that finally, on some day, we will be able to use Internet with all its potential benefits without any fear of security risk with the help of technology like Sandbox.
Screen Shot Descriptions:
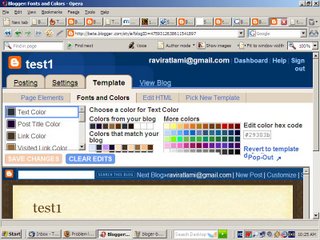
1. sand01.jpg Finjan Software’s Surfin Guard, the premier sandbox software that guards your computer from malicious code downloaded across Internet – installs without much interaction.
2. sand02.jpg Finjan Software’s SurfinGuard need Java Runtime Environment installed in your computer.
3. sand03.jpg SurfinGuard supports latest applications and OS including Windows XP
4. sand04.jpg SurfinGuard, the proactive defence against malicious code starts with Windows and guards your computer constantly in background unless you turn it off.
5. sand05.jpg SurfinGuard can also monitor host applications that includes FTP, Instant Messengers, Mail Clients etc.
6. sand06.jpg SurfinGuard can block sites that try to read file from your computer including porn sites.
7. sand07.jpg You can set security policy to low, high or Medium as per your security requirements.
8. sand08.jpg With the help of SurfinGuard, individual code content (executables, ActiveX, Java Applets, JavaScript etc.) execution can be set to allow, block or monitor for your security requirements.
9. sand09.jpg Behavior of standalone application can also be watched and blocked for any malicious action that include genuine program’s buggy actions.
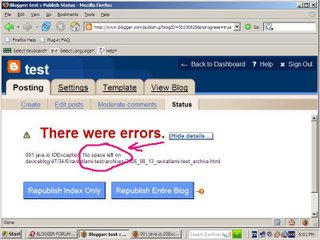
10. sand10.jpg Pelican Security’s Sandbox software “SafeTnet” is a powerful security tool.
11. sand11.jpg You get alerts for applications that cannot be monitored by SafeTnet due to any reason such as version incompatibility etc.
12. sand12.jpg You can set trusted sites / other downloads and web applications to exclude monitoring from SafeTnet.
13. sand13.jpg SafeTnet’s custom security settings let you assign to allow deny or prompt virtually every file manipulations.
14. sand14.jpg Through SafeTnet’s alert settings, you can set it to send alert email at remote end for remote surveillance.
15. sand15.jpg Sandbox application like surfinGuard can log web activities performed by your computer for further analysis.
16. sand16.jpg SurfinGuard instantly detects the policy violations caused by web site’s applets / scripts. It also shows the current running process / web sites in its menu bar.
17. sand17.jpg Individual security settings for e-mail / FTP / Instant Messenger and Web Browser can be assigned through SafeTnet.